This guide walks you through installing the Social Engineering Toolkit (SET) in Kali Linux Light, a lightweight version of Kali ideal for low-resource systems. You’ll learn how to set up SET, run it securely, and troubleshoot common issues—all with clear, beginner-friendly instructions.
Key Takeaways
- Step-by-step: Easy to follow instructions
Introduction: What You’ll Learn in This Guide
If you’re diving into ethical hacking or cybersecurity, you’ve probably heard of the Social Engineering Toolkit (SET)—a powerful open-source tool designed to simulate real-world social engineering attacks. From phishing emails to malicious websites, SET helps security professionals test human vulnerabilities in a controlled environment. But what if you’re using Kali Linux Light, the streamlined version of Kali built for low-end machines? Unlike the full Kali Linux distribution, Kali Light doesn’t come with SET pre-installed. That’s where this guide comes in.
In this comprehensive how-to, you’ll learn how to install Social Engineering Toolkit in Kali Linux Light from scratch. We’ll cover everything from updating your system and installing dependencies to launching SET and running your first attack simulation. Whether you’re a student, a cybersecurity enthusiast, or a professional tester, this guide is designed to be beginner-friendly while still offering depth for more experienced users. By the end, you’ll have SET up and running smoothly—even on older hardware.
What Is Kali Linux Light?
Before we jump into the installation, let’s clarify what Kali Linux Light actually is. Kali Linux Light is a minimal version of the popular penetration testing OS, designed for systems with limited resources. It strips away the graphical desktop environment and many pre-installed tools, leaving only the core system and essential utilities. This makes it perfect for running on older laptops, virtual machines with low RAM, or even single-board computers like the Raspberry Pi.
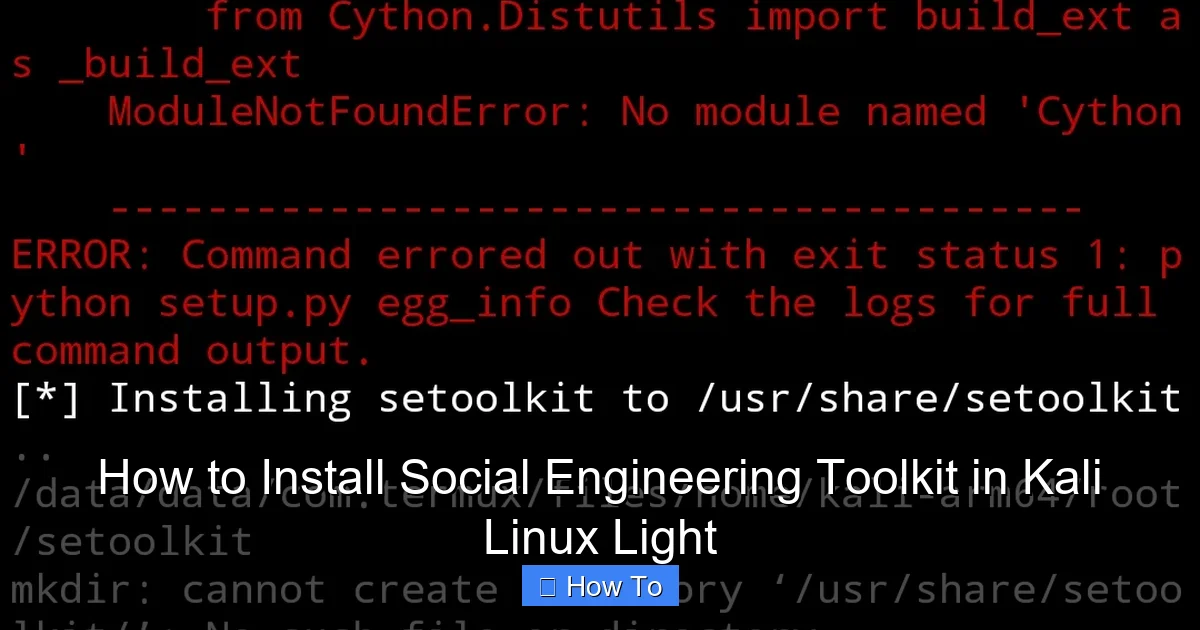
Visual guide about How to Install Social Engineering Toolkit in Kali Linux Light
Image source: cdn.educba.com
While Kali Light is lightweight and fast, it also means you have to manually install most tools—including the Social Engineering Toolkit. That’s both a challenge and an opportunity: you get full control over what’s installed, but you also need to know how to set things up properly. The good news? Once you’ve installed SET, it works just as well as it does on the full Kali distribution.
Why Use the Social Engineering Toolkit?
The Social Engineering Toolkit is one of the most widely used tools in ethical hacking. Developed by TrustedSec, SET automates many common social engineering attack vectors, making it easier to simulate real-world threats. Here are a few reasons why SET is so valuable:
- Phishing simulations: Create fake login pages that mimic Google, Facebook, or banking sites to test user awareness.
- Credential harvesting: Capture usernames and passwords entered into cloned websites.
- Malware delivery: Embed payloads into files or links to demonstrate how malware spreads.
- Website cloning: Replicate legitimate websites with a single command.
- Multi-platform support: Works on Windows, macOS, and Linux targets.
SET is especially useful for red team exercises, security training, and awareness campaigns. It helps organizations understand how easily attackers can exploit human behavior—not just technical flaws. But remember: with great power comes great responsibility. Always use SET in legal, authorized environments.
Prerequisites: What You Need Before Starting
Before we begin the installation, make sure your system meets the following requirements:
- Kali Linux Light installed: You should already have Kali Light running, either on physical hardware or in a virtual machine.
- Internet connection: You’ll need to download packages and dependencies.
- Basic terminal knowledge: Familiarity with Linux commands like
sudo,apt, andcdis helpful. - At least 1GB of RAM: While Kali Light is lightweight, SET and its dependencies may require extra memory.
- Root or sudo access: You’ll need administrative privileges to install software.
If you’re running Kali Light in a virtual machine (like VirtualBox or VMware), ensure that your network adapter is set to “Bridged” or “NAT” mode so the VM can access the internet.
Step 1: Update Your Kali Linux Light System
The first step in any Linux installation process is to update your system. This ensures you have the latest security patches, bug fixes, and package versions. Outdated systems can lead to dependency conflicts and failed installations.
Open the Terminal
Launch the terminal by pressing Ctrl + Alt + T or by searching for “Terminal” in your application menu.
Run System Update Commands
Type the following commands one by one and press Enter after each:
sudo apt update sudo apt upgrade -y sudo apt dist-upgrade -y
Let’s break down what these commands do:
sudo apt update: Refreshes the list of available packages from the repositories.sudo apt upgrade -y: Installs the latest versions of all installed packages. The-yflag automatically answers “yes” to prompts.sudo apt dist-upgrade -y: Handles dependency changes and may install or remove packages as needed.
This process may take a few minutes, depending on your internet speed and how long it’s been since your last update. Once complete, your system will be ready for the next step.
Optional: Clean Up Unnecessary Packages
To free up space and keep your system lean, run:
sudo apt autoremove -y sudo apt autoclean
These commands remove unused dependencies and clear the package cache.
Step 2: Install Required Dependencies
The Social Engineering Toolkit relies on several Python libraries and system tools to function properly. Since Kali Light is minimal, many of these may not be installed by default. Let’s install them now.
Install Python 2.7 and pip
Even though Python 2 is deprecated, SET still uses it. Install it with:
sudo apt install python2.7 python2.7-dev -y
Next, install pip for Python 2, which is needed to manage Python packages:
curl https://bootstrap.pypa.io/pip/2.7/get-pip.py --output get-pip.py sudo python2.7 get-pip.py
This downloads and runs the official pip installer for Python 2.7.
Install Additional Dependencies
SET requires several other packages. Install them all at once:
sudo apt install git apache2 python3-pip python3-venv -y sudo pip2 install pyopenssl pycrypto
Here’s what each package does:
- git: Used to clone the SET repository from GitHub.
- apache2: Web server needed to host phishing pages.
- python3-pip and python3-venv: Useful for managing Python 3 environments (some SET modules may use Python 3).
- pyopenssl and pycrypto: Cryptographic libraries required for secure connections and payload encryption.
After installation, verify that Python 2.7 and pip are working:
python2.7 --version pip2 --version
You should see version numbers confirming the installations.
Step 3: Download the Social Engineering Toolkit
Now that your system is ready, it’s time to download SET. The official repository is hosted on GitHub, so we’ll use git to clone it.
Clone the SET Repository
In your terminal, navigate to your home directory (if you’re not already there):
cd ~
Then clone the SET repository:
git clone https://github.com/trustedsec/social-engineer-toolkit set/
This creates a folder named set in your home directory containing all the SET files.
Verify the Download
Check that the files were downloaded correctly:
ls -la ~/set
You should see files like set.py, README.md, and folders like src and config.
Set Proper Permissions
Ensure the SET directory is executable:
sudo chmod -R 755 ~/set sudo chown -R $USER:$USER ~/set
This gives your user account full access to the files.
Step 4: Install SET Using the Setup Script
SET comes with a built-in installer that handles most of the configuration automatically. Let’s run it.
Navigate to the SET Directory
cd ~/set
Run the Installer
sudo python2.7 setup.py install
This script installs SET system-wide and sets up necessary configurations. It may take a minute or two to complete.
What the Installer Does
The setup script performs several tasks:
- Installs required Python modules.
- Configures Apache web server settings.
- Sets up SSL certificates for secure phishing pages.
- Creates desktop shortcuts (if a GUI is available).
If you see any errors during installation, don’t panic—we’ll cover troubleshooting in a later section.
Step 5: Launch the Social Engineering Toolkit
Now for the moment of truth: launching SET.
Start SET from the Terminal
sudo setoolkit
The first time you run it, SET will display a license agreement. Read it carefully, then type YES to accept.
Choose Your Language
SET will ask for your preferred language. Press 1 for English (or your preferred option).
Main Menu Appears
You should now see the SET main menu, which looks something like this:
Select from the menu: 1) Social-Engineering Attacks 2) Penetration Testing (Fast-Track) 3) Third Party Modules 4) Update the Social-Engineer Toolkit 5) Update SET configuration 6) View past generated reports 7) Exit the Social-Engineer Toolkit
Congratulations! You’ve successfully installed and launched SET on Kali Linux Light.
Step 6: Configure Apache and Test a Basic Attack
To make sure everything is working, let’s run a simple phishing simulation.
Start Apache Web Server
sudo service apache2 start
Verify it’s running:
sudo service apache2 status
You should see “active (running)” in green.
Run a Website Cloning Attack
In SET, choose:
1) Social-Engineering Attacks 2) Website Attack Vectors 3) Credential Harvester Attack Method 4) Site Cloner
When prompted, enter the URL of a website you want to clone (e.g., https://www.google.com). SET will download the site and host a copy on your local server.
Access the Cloned Site
Open a web browser and go to:
http://localhost
You should see a cloned version of the website. This confirms that SET and Apache are working correctly.
Troubleshooting Common Issues
Even with careful installation, you might run into problems. Here are some common issues and how to fix them.
Issue 1: “Command not found: setoolkit”
If you get this error, it means SET wasn’t installed correctly. Try reinstalling:
cd ~/set sudo python2.7 setup.py install
Also, ensure the setoolkit script is in your PATH. You can run it directly with:
sudo python2.7 ~/set/set.py
Issue 2: Apache Fails to Start
If Apache won’t start, check for port conflicts:
sudo netstat -tulnp | grep :80
If another service is using port 80, stop it or reconfigure Apache.
Issue 3: Missing Python Modules
If SET complains about missing modules, install them manually:
sudo pip2 install [module_name]
Common modules include pexpect, mechanize, and pyopenssl.
Issue 4: SSL Certificate Errors
Some attacks require valid SSL certificates. Generate a self-signed cert:
sudo openssl req -new -x509 -keyout /etc/ssl/private/apache-selfsigned.key -out /etc/ssl/certs/apache-selfsigned.crt -days 365 -nodes
Then configure Apache to use it.
Best Practices and Security Tips
Now that SET is installed, keep these tips in mind:
- Always use SET in a lab environment: Never test on real users without permission.
- Keep SET updated: Run
git pullin the~/setdirectory regularly. - Use a virtual machine: Isolate your testing environment to avoid accidental damage.
- Disable SET when not in use: Stop Apache and close SET to reduce attack surface.
- Log your activities: Keep records of tests for reporting and auditing.
Conclusion: You’re Ready to Use SET
Installing the Social Engineering Toolkit in Kali Linux Light may seem daunting at first, but with this guide, you’ve successfully set it up from scratch. You’ve updated your system, installed dependencies, cloned the SET repository, and launched your first attack simulation. Whether you’re learning ethical hacking or conducting professional penetration tests, SET is a powerful tool in your arsenal.
Remember, the goal of social engineering testing is to improve security—not to exploit it. Use SET responsibly, stay within legal boundaries, and always prioritize ethics. With practice, you’ll become proficient in simulating real-world attacks and helping organizations defend against them.
Now go ahead, explore SET’s features, and start building your cybersecurity skills. The digital world needs more ethical hackers—and you’re on your way to becoming one.